- Browse
- Authentication Methods
Results for "authentication methods"
 Status: NewNewStatus: Free TrialFree Trial
Status: NewNewStatus: Free TrialFree TrialSkills you'll gain: Kubernetes, Network Troubleshooting, Authentications, Debugging, Event Monitoring, System Monitoring, Application Deployment, API Design, Application Programming Interface (API), Command-Line Interface
Intermediate · Course · 1 - 4 Weeks
 Status: NewNewStatus: Free TrialFree Trial
Status: NewNewStatus: Free TrialFree TrialSkills you'll gain: Java Programming, Java, Object Oriented Programming (OOP), Oracle SQL Developer, Oracle Databases
Intermediate · Specialization · 1 - 3 Months
 Status: PreviewPreview
Status: PreviewPreviewSkills you'll gain: Mechanical Engineering, Thermal Management, Engineering Analysis, Simulations, Numerical Analysis, Engineering, Mathematical Modeling, Physics
Intermediate · Course · 1 - 3 Months
 G
GGoogle Cloud
Skills you'll gain: Role-Based Access Control (RBAC), Kubernetes, Authorization (Computing), Identity and Access Management, User Accounts, Containerization, Development Environment, Cloud Engineering
Intermediate · Project · Less Than 2 Hours
 Status: NewNewStatus: PreviewPreviewS
Status: NewNewStatus: PreviewPreviewSSkillsBooster Academy
Skills you'll gain: Email Marketing, Lead Generation, Email Automation, Customer Relationship Management (CRM) Software, Performance Metric, Sales Pipelines, Digital Marketing, Copywriting, Customer Support, Customer Engagement, Data Pipelines, Compliance Management, Revenue Cycle Management, Generative AI, Design and Product, Product Design, Law, Regulation, and Compliance, Artificial Intelligence, Design Elements And Principles, Statistics
Beginner · Course · 1 - 3 Months

Skills you'll gain: Computer Vision, Python Programming, Image Analysis, Real Time Data, Classification Algorithms, Development Environment, Deep Learning, Software Installation, Algorithms
Beginner · Course · 3 - 6 Months
 Status: NewNewStatus: Free TrialFree Trial
Status: NewNewStatus: Free TrialFree TrialSkills you'll gain: Active Directory, Software Installation, System Configuration, Microsoft Intune (Mobile Device Management Software), Azure Active Directory, Hyper-V, Enterprise Architecture, System Implementation, Infrastructure Architecture, Configuration Management, IT Infrastructure, Mac OS, Microsoft Azure, System Requirements, Scalability
Intermediate · Course · 1 - 4 Weeks
 Status: NewNewStatus: Free TrialFree TrialL
Status: NewNewStatus: Free TrialFree TrialLLearnQuest
Skills you'll gain: Cyber Threat Hunting, Incident Response, Cyber Threat Intelligence, Security Information and Event Management (SIEM), Intrusion Detection and Prevention, Threat Detection, Anomaly Detection, AI Security, Scripting, Cyber Operations, Event Monitoring, Network Analysis, Automation, Data Preprocessing, Machine Learning Algorithms
Beginner · Course · 1 - 4 Weeks
 Status: NewNewStatus: PreviewPreview
Status: NewNewStatus: PreviewPreviewSkills you'll gain: Time Series Analysis and Forecasting, Forecasting, Predictive Modeling, R Programming, Regression Analysis, Business Analytics, Trend Analysis, Statistical Analysis, Statistical Modeling, Analysis, Model Evaluation
Mixed · Course · 1 - 4 Weeks
 Status: NewNewStatus: Free TrialFree Trial
Status: NewNewStatus: Free TrialFree TrialSkills you'll gain: Malware Protection, Network Security, Information Systems Security, Security Controls, Cybersecurity, Data Security, Mobile Security, Computer Security Awareness Training, Wireless Networks, Authentications, Human Factors (Security), Threat Detection, Encryption, User Accounts
Intermediate · Course · 1 - 4 Weeks
 Status: Free TrialFree TrialD
Status: Free TrialFree TrialDDartmouth College
Skills you'll gain: Operations Research, Analytics, Business Analytics, Process Optimization, Data-Driven Decision-Making, Strategic Decision-Making, Data Science, Feature Engineering, Complex Problem Solving, Logistics, Model Evaluation, Python Programming, Decision Making, Cloud Computing
Intermediate · Course · 1 - 3 Months
 Status: Free TrialFree TrialS
Status: Free TrialFree TrialSScrimba
Skills you'll gain: Application Deployment, Continuous Deployment, Web Development Tools, Continuous Delivery, Release Management, React.js, Vue.JS, Code Review
Beginner · Course · 1 - 4 Weeks
In summary, here are 10 of our most popular authentication methods courses
- Certified Kubernetes Application Developer (CKAD): Unit 6: Pearson
- Exam Prep: Oracle Certified Associate, Java SE 8 [1Z0-808]: Whizlabs
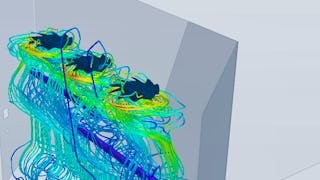
- Angewandte numerische Fluiddynamik: Siemens
- Using Role-based Access Control in Kubernetes Engine: Google Cloud
- Email Marketing: Boost Sales with High-Converting Campaigns: SkillsBooster Academy
- Computer Vision: Face Recognition Quick Starter in Python: Packt
- SCCM Installation & Client Configuration: Packt
- GenAI for Cybersecurity: Blue Team: LearnQuest
- Master Time Series Forecasting with R: Analyze & Predict: EDUCBA
- A+ Core 2 V15 - Pearson Cert Prep: Unit 2: Pearson










