- Browse
- Threat Detection
Results for "threat detection"
 Status: Free TrialFree TrialU
Status: Free TrialFree TrialUUniversity of Colorado Boulder
Skills you'll gain: Statistical Analysis, Matplotlib, Regression Analysis, Statistical Modeling, Data Science, Data Analysis, Data Visualization, Pandas (Python Package), Anomaly Detection, Time Series Analysis and Forecasting, Data Visualization Software, Data Collection, Data Manipulation, Application Programming Interface (API)
Build toward a degree
4.3·Rating, 4.3 out of 5 stars6 reviewsIntermediate · Course · 1 - 4 Weeks
 Status: Free TrialFree TrialB
Status: Free TrialFree TrialBBoard Infinity
Skills you'll gain: Incident Response, Risk Management Framework, Cyber Risk, Risk Management, Security Management, Enterprise Risk Management (ERM), Business Risk Management, Cyber Threat Intelligence, Governance Risk Management and Compliance, Continuous Monitoring, Cyber Security Strategy, Security Information and Event Management (SIEM), Threat Detection, ISO/IEC 27001, Control Objectives for Information and Related Technology (COBIT), Key Performance Indicators (KPIs)
4.9·Rating, 4.9 out of 5 stars9 reviewsIntermediate · Course · 1 - 4 Weeks
 Status: FreeFreeD
Status: FreeFreeDDeepLearning.AI
Skills you'll gain: Retrieval-Augmented Generation, Vector Databases, Anomaly Detection, Embeddings, LLM Application, Semantic Web, Application Design, Natural Language Processing, Image Analysis, AI Personalization
4.2·Rating, 4.2 out of 5 stars16 reviewsBeginner · Project · Less Than 2 Hours
 Status: Free TrialFree Trial
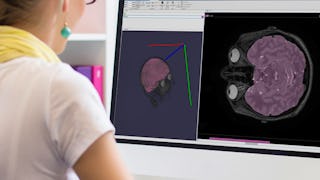
Status: Free TrialFree TrialSkills you'll gain: Image Analysis, Image Quality, Matlab, Computer Vision, Digital Signal Processing, Spatial Data Analysis, Medical Imaging, Spatial Analysis, Algorithms
4.8·Rating, 4.8 out of 5 stars53 reviewsBeginner · Course · 1 - 4 Weeks
 Status: Free TrialFree TrialL
Status: Free TrialFree TrialLLearnKartS
Skills you'll gain: Workplace Bullying Intervention, Workplace inclusivity, Safety Culture, Accountability, Responsible AI, Compliance Management, Social Media
4.7·Rating, 4.7 out of 5 stars170 reviewsBeginner · Course · 1 - 4 Weeks
 Status: Free TrialFree TrialJ
Status: Free TrialFree TrialJJohns Hopkins University
Skills you'll gain: Social Network Analysis, Network Analysis, Data Visualization, Graph Theory, Relational Databases, Data Visualization Software, Data Storytelling, Data Analysis, Social Sciences, Statistical Analysis, Machine Learning, R Programming, Analytical Skills, Sociology, Natural Language Processing, Data Manipulation, Text Mining, Analytics, Social Impact, Statistical Modeling
4.3·Rating, 4.3 out of 5 stars16 reviewsIntermediate · Specialization · 3 - 6 Months
 A
AAmazon Web Services
Skills you'll gain: Infrastructure as Code (IaC), Amazon CloudWatch, CI/CD, AWS CloudFormation, Application Deployment, Continuous Deployment, Cloud Deployment, Amazon Web Services, Continuous Integration, Model Deployment, DevOps, Cloud Management, Generative AI, Cloud Applications, System Monitoring, Automation, Continuous Monitoring
4.4·Rating, 4.4 out of 5 stars11 reviewsBeginner · Course · 1 - 4 Weeks
 Status: Free TrialFree Trial
Status: Free TrialFree TrialSkills you'll gain: Recurrent Neural Networks (RNNs), PyTorch (Machine Learning Library), Convolutional Neural Networks, Deep Learning, Classification Algorithms, Transfer Learning, Applied Machine Learning, Image Analysis, Model Evaluation, Artificial Neural Networks, Computer Vision, Data Preprocessing
4.9·Rating, 4.9 out of 5 stars9 reviewsIntermediate · Course · 1 - 3 Months
 Status: Free TrialFree TrialL
Status: Free TrialFree TrialLLearnQuest
Skills you'll gain: Threat Modeling, IT Security Architecture, Threat Detection, Security Engineering, Internet Of Things, Network Security, Infrastructure Security, Security Controls, Data Security, Cryptographic Protocols, Vulnerability Assessments, Risk Management Framework, Cloud Computing
4.7·Rating, 4.7 out of 5 stars7 reviewsIntermediate · Course · 1 - 4 Weeks
 Status: PreviewPreviewU
Status: PreviewPreviewUUniversity of Geneva
Skills you'll gain: General Science and Research, Scientific Methods, Scientific Visualization, Research, Quantitative Research, Physics, Mathematical Modeling, Simulations, Mechanics, Chemistry
4.7·Rating, 4.7 out of 5 stars38 reviewsIntermediate · Course · 1 - 3 Months
 Status: NewNewStatus: Free TrialFree TrialM
Status: NewNewStatus: Free TrialFree TrialMMacquarie University
Skills you'll gain: Incident Response, Incident Management, Cyber Governance, Computer Security Incident Management, Security Awareness, Cyber Security Strategy, Law, Regulation, and Compliance, Cyber Attacks, Security Management, Security Strategy, Culture Transformation, Cyber Security Policies, Intrusion Detection and Prevention, Threat Detection, Mobile Security, Disaster Recovery, Cybersecurity, Cyber Risk, Cyber Operations, Cyber Security Assessment
4.7·Rating, 4.7 out of 5 stars25 reviewsBeginner · Specialization · 3 - 6 Months
 Status: NewNewStatus: Free TrialFree TrialM
Status: NewNewStatus: Free TrialFree TrialMMacquarie University
Skills you'll gain: Incident Response, Incident Management, Threat Modeling, Cyber Governance, Computer Security Incident Management, Cyber Security Strategy, Cyber Attacks, Security Management, Threat Management, Cyber Risk, Cyber Security Policies, Cybersecurity, Intrusion Detection and Prevention, Governance Risk Management and Compliance, Cyber Security Assessment, Cyber Operations, Compliance Management, Governance, Risk Management, Risk Control
4.7·Rating, 4.7 out of 5 stars12 reviewsBeginner · Specialization · 3 - 6 Months
Searches related to threat detection
In summary, here are 10 of our most popular threat detection courses
- Modeling Climate Anomalies with Statistical Analysis: University of Colorado Boulder
- Advanced Cybersecurity Risk Management: Board Infinity
- Building Applications with Vector Databases: DeepLearning.AI
- Image Segmentation, Filtering, and Region Analysis: MathWorks
- POSH - Prevention of Sexual Harassment: LearnKartS
- Social Media Analytics: Johns Hopkins University
- DevOps and AI on AWS: CI/CD for Generative AI Applications: Amazon Web Services
- Building and Training Neural Networks with PyTorch: Packt
- Foundations of Secure IoT Architecture: LearnQuest
- The Diversity of Exoplanets: University of Geneva










