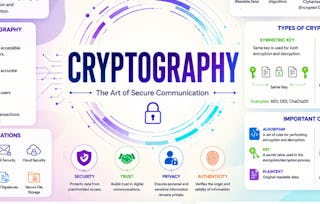
This course will introduce you to the foundations of modern cryptography, with an eye toward practical applications.

Cryptography
Ends soon! Save on skills that make you shine with 40% off 3 months of Coursera Plus. Save now

1,324 reviews
Details to know

Add to your LinkedIn profile
8 assignments
See how employees at top companies are mastering in-demand skills

There are 7 modules in this course
Instructor

Offered by
Explore more from Computer Security and Networks
 Status: Preview
Status: PreviewUniversity of Leeds
 Status: Preview
Status: PreviewBirla Institute of Technology & Science, Pilani
 Status: Preview
Status: PreviewBirla Institute of Technology & Science, Pilani
 Status: Preview
Status: PreviewUniversity of London
Why people choose Coursera for their career

Felipe M.

Jennifer J.

Larry W.

Chaitanya A.
Learner reviews
- 5 stars
71.75%
- 4 stars
21.67%
- 3 stars
3.85%
- 2 stars
1.51%
- 1 star
1.20%
Showing 3 of 1324
Reviewed on Feb 23, 2020
It is a delightful experience to take this course. I could really understand the insights of Cryptography in a better manner.
Reviewed on Feb 15, 2016
I felt it was a good introduction to cryptography. There were quizzes and programming assignments throughout the course to assess knowledge.
Reviewed on Nov 12, 2016
Good course, but can get very deep at times, especially near the middle of the course.The first 2 weeks are rather simple, week 3 is okay, 4 and 5 are very detailed, and 6 and 7 are easier.





