- Browse
- Security Requirements Analysis
Results for "security requirements analysis"

Skills you'll gain: Backlogs, Requirements Management, Business Requirements, Performance Measurement, Requirements Analysis, Business Analysis, Root Cause Analysis, Change Requests, Data Mining, Performance Analysis, Jira (Software), Data-Driven Decision-Making, Analysis, Prioritization
★ 4.8 (66) · Intermediate · Course · 1 - 4 Weeks
Skills you'll gain: Cyber Threat Intelligence, Cyber Attacks, Regulatory Requirements, Cyber Security Policies, Cyber Security Assessment, Financial Industry Regulatory Authorities, Continuous Monitoring, Regulatory Compliance, Governance Risk Management and Compliance, Risk Analysis, Data Ethics, Emerging Technologies, Cloud Security, AI Security, Blockchain
Beginner · Course · 1 - 4 Weeks

Skills you'll gain: Application Security, Cyber Security Strategy, Patch Management
★ 4.3 (6) · Intermediate · Course · 1 - 4 Weeks

Skills you'll gain: IT Security Architecture, Endpoint Security, Zero Trust Network Access, Application Security, Security Strategy, Hardening, Microsoft Servers, Data Security, Security Management, Vulnerability Scanning, Patch Management
Advanced · Course · 1 - 4 Weeks
 C
CCisco Learning and Certifications
Skills you'll gain: Cyber Threat Intelligence, Cyber Threat Hunting, Threat Detection, Vulnerability Assessments, Threat Management, Event Monitoring, Intrusion Detection and Prevention, Security Information and Event Management (SIEM), Computer Security Incident Management, Continuous Monitoring, Incident Response, Security Awareness, Security Management, Malware Protection, Network Security, Network Analysis, Network Monitoring
★ 4.8 (40) · Mixed · Course · 1 - 4 Weeks
 C
CCertNexus
Skills you'll gain: Threat Modeling, Cybersecurity, Cyber Threat Intelligence, Threat Management, Information Systems Security, Threat Detection, Security Management, Cyber Risk, Cyber Security Strategy, Cyber Security Assessment, Risk Analysis, Computer Security, Risk Mitigation, Risk Management, Network Security, Risk Management Framework, Enterprise Risk Management (ERM), Risk Appetite, Trend Analysis, Technical Documentation
Mixed · Course · 1 - 4 Weeks

Skills you'll gain: MITRE ATT&CK Framework, Threat Modeling, Secure Coding, Application Security, Threat Management, Cryptography, Encryption, Cyber Security Assessment, Cybersecurity, Security Strategy, Authorization (Computing), Security Controls, Internet Of Things, Identity and Access Management, Asset Management
★ 4.6 (98) · Beginner · Course · 1 - 4 Weeks

Skills you'll gain: Requirements Elicitation, User Story, Business Requirements, Business Analysis, Process Modeling, Requirements Analysis, Financial Analysis, Requirements Management, Business Process Modeling, Stakeholder Engagement, Interviewing Skills, Analysis, Discussion Facilitation, Stakeholder Communications, Collaboration, Communication
★ 4.9 (80) · Intermediate · Course · 1 - 4 Weeks

Skills you'll gain: AI Security, Threat Modeling, Secure Coding, Vulnerability Scanning, Penetration Testing, Vulnerability Management, Dependency Analysis, Application Security, Cyber Security Assessment, Security Requirements Analysis, DevSecOps, Code Review, Risk Management Framework
Intermediate · Course · 1 - 4 Weeks

Skills you'll gain: IT Security Architecture, Threat Modeling, Enterprise Architecture, Security Architecture Review, Cybersecurity, Application Security, Cyber Security Strategy, Network Security, Systems Architecture, Identity and Access Management, Information Systems Security, Endpoint Security, Data Security, Risk Analysis, Remote Access Systems, Risk Mitigation, Case Studies, Risk Management, Business Requirements
★ 4.7 (6) · Intermediate · Course · 1 - 3 Months

Skills you'll gain: Microsoft Azure, Cloud Security, IT Security Architecture, DevSecOps, Threat Management, Zero Trust Network Access, Cloud Solutions, Cloud Computing Architecture, Cyber Security Strategy, Security Architecture Review, Azure DevOps Pipelines, Cloud Standards, Cloud Computing, Threat Detection, Security Controls, Security Strategy
Intermediate · Course · 1 - 4 Weeks

Skills you'll gain: IT Security Architecture, Threat Modeling, Application Security, Cloud Deployment, Cloud Computing Architecture, Cloud Computing, Cloud Services, Security Engineering, Cloud Security, Systems Architecture, Security Controls, Software As A Service, Infrastructure As A Service (IaaS), Computer Security, Data Security, Platform As A Service (PaaS), Data Integrity
★ 5 (13) · Advanced · Course · 1 - 4 Weeks
In summary, here are 10 of our most popular security requirements analysis courses
- Advanced Requirements Management & Solution Evaluation: Starweaver
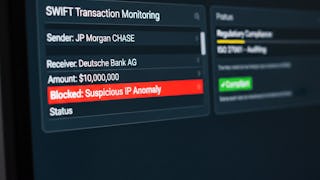
- Analyze Cybersecurity Risks in Financial Systems: EDUCBA
- CompTIA Cybersecurity Analyst (CySA+) CS0-003: Unit 2: Pearson
- Design security solutions for infrastructure: Whizlabs
- Threat Investigation: Cisco Learning and Certifications
- CFR: Risk and Threat Analysis: CertNexus
- Advanced Cybersecurity Concepts and Capstone Project: Microsoft
- Advanced Business Analysis: Elicitation & Analysis: Starweaver
- Evaluate, Create, and Analyze App Security: Coursera
- Cybersecurity Architecture Fundamentals: Packt










