- Browse
- Attack Classification And Analysis
Results for "attack classification and analysis"
 Status: Free TrialFree Trial
Status: Free TrialFree TrialSkills you'll gain: Cryptography, Encryption, Brute-force attacks, Python Programming, Programming Principles, Computational Logic, Program Development, Algorithms, Code Reusability, File I/O, File Management
Mixed · Course · 1 - 4 Weeks
 Status: Free TrialFree Trial
Status: Free TrialFree TrialSkills you'll gain: Penetration Testing, Cyber Security Assessment, Security Testing, Exploitation techniques, Hardening, Vulnerability Assessments, Intrusion Detection and Prevention, Brute-force attacks, Application Security, Network Security, Virtual Local Area Network (VLAN), Business Logic, Cloud Security, API Testing, Wireless Networks, Data Persistence, Application Programming Interface (API)
Advanced · Course · 1 - 4 Weeks
 Status: NewNewStatus: PreviewPreview
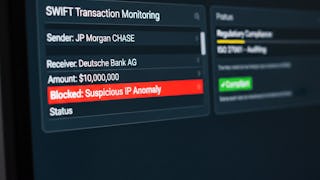
Status: NewNewStatus: PreviewPreviewSkills you'll gain: Cyber Threat Intelligence, Cyber Attacks, Cyber Security Policies, Regulatory Requirements, Cyber Security Assessment, Financial Industry Regulatory Authorities, Continuous Monitoring, Regulatory Compliance, Governance Risk Management and Compliance, Risk Analysis, Data Ethics, Emerging Technologies, Cloud Security, AI Security, Blockchain
Beginner · Course · 1 - 4 Weeks
 Status: Free TrialFree Trial
Status: Free TrialFree TrialSkills you'll gain: Penetration Testing, Exploit development, Exploitation techniques, Security Testing, Brute-force attacks, Vulnerability Assessments, Authentications, Wireless Networks, Network Security, Linux, Encryption, Microsoft Windows, Network Analysis, Data Persistence
Mixed · Course · 1 - 4 Weeks
 Status: Free TrialFree TrialJ
Status: Free TrialFree TrialJJohns Hopkins University
Skills you'll gain: Model Evaluation, Intrusion Detection and Prevention, Threat Detection, Computer Security Incident Management, Cybersecurity, Model Training, Incident Response, Machine Learning Methods, Anomaly Detection, Applied Machine Learning, Continuous Monitoring, AI Security, Cryptographic Protocols, Network Security, Machine Learning Algorithms, Machine Learning, Predictive Modeling, Network Architecture, Unsupervised Learning, Supervised Learning
Intermediate · Course · 1 - 3 Months

Skills you'll gain: Cyber Threat Intelligence, Vulnerability Assessments, Incident Response, Cyber Security Assessment, Vulnerability Scanning, Cybersecurity, Threat Modeling, Threat Detection, Application Security, Malware Protection, Network Analysis, Encryption
Intermediate · Course · 3 - 6 Months
 Status: Free TrialFree TrialU
Status: Free TrialFree TrialUUniversity of Colorado Boulder
Skills you'll gain: Penetration Testing, Network Security, Cyber Operations, Network Monitoring, Exploitation techniques, Vulnerability Scanning, Cryptographic Protocols, Remote Access Systems, Network Protocols, Encryption, General Networking, Command-Line Interface, Network Analysis, Proxy Servers
Build toward a degree
4.7·Rating, 4.7 out of 5 stars13 reviewsIntermediate · Course · 1 - 3 Months
 Status: NewNewStatus: PreviewPreview
Status: NewNewStatus: PreviewPreviewSkills you'll gain: Cyber Threat Intelligence, Threat Modeling, MITRE ATT&CK Framework, Threat Detection, Threat Management, Intelligence Collection and Analysis, Report Writing, Technical Communication, Cyber Security Strategy, Cybersecurity, Research Reports, Data Storytelling, Oral Expression, Verbal Communication Skills, Incident Response, Risk Analysis, Communication, Infrastructure Security, Analysis, Stakeholder Communications
Intermediate · Course · 1 - 3 Months
 Status: NewNewStatus: PreviewPreviewS
Status: NewNewStatus: PreviewPreviewSStarweaver
Skills you'll gain: Cyber Threat Hunting, Splunk, Threat Detection, Jupyter, Anomaly Detection, Threat Management, Cybersecurity, Data Analysis, Data Science, Data Wrangling, Applied Machine Learning, Security Information and Event Management (SIEM), Data Cleansing, Data Transformation, Data Preprocessing, MLOps (Machine Learning Operations), Unsupervised Learning, Automation
Intermediate · Course · 1 - 3 Months
 Status: Free TrialFree TrialS
Status: Free TrialFree TrialSSimplilearn
Skills you'll gain: Distributed Denial-Of-Service (DDoS) Attacks, Cybersecurity, Cyber Attacks, Threat Detection, Exploitation techniques, Malware Protection, Security Awareness, SQL, Databases
Beginner · Course · 1 - 4 Weeks
 Status: Free TrialFree TrialJ
Status: Free TrialFree TrialJJohns Hopkins University
Skills you'll gain: Generative Adversarial Networks (GANs), AI Security, Fraud detection, Model Evaluation, Feature Engineering, Cybersecurity, Cyber Security Strategy, Reinforcement Learning, Model Optimization, Data Synthesis
4.4·Rating, 4.4 out of 5 stars24 reviewsIntermediate · Course · 1 - 3 Months
 Status: Free TrialFree TrialU
Status: Free TrialFree TrialUUniversity of Colorado System
Skills you'll gain: Public Key Infrastructure, Cybersecurity, Information Systems Security, Data Security, Cyber Attacks, Information Assurance, Network Security, Risk Management Framework, Security Controls, Cryptography, Cryptographic Protocols, Key Management, Security Engineering, Threat Modeling, Security Management, Authorization (Computing), Encryption, Email Security, Data Integrity, Authentications
3.9·Rating, 3.9 out of 5 stars241 reviewsIntermediate · Course · 1 - 4 Weeks
In summary, here are 10 of our most popular attack classification and analysis courses
- Python Cryptography: Analyze & Break Ciphers: EDUCBA
- Advanced Penetration Techniques: Packt
- Analyze Cybersecurity Risks in Financial Systems: EDUCBA
- Ethical Hacking with Kali Linux: Analyze & Apply: EDUCBA
- Machine Learning and Emerging Technologies in Cybersecurity: Johns Hopkins University
- TOTAL - CompTIA CySA+ Cybersecurity Analyst (CS0-003): Packt
- Security & Ethical Hacking: Attacking the Network: University of Colorado Boulder
- Advanced Strategic Threat Intelligence Research & Reporting: Starweaver
- Threat Hunting Techniques: Starweaver
- Cyber Threats Training for Beginners : Simplilearn










