Filter by
The language used throughout the course, in both instruction and assessments.
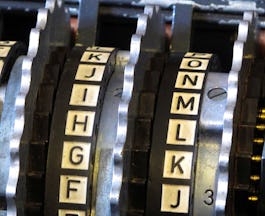
79 results for "cryptographic hardware"

University of Maryland, College Park
Skills you'll gain: Security Engineering, Cyberattacks, Security Software, Security Strategy, Software Security, Cryptography, Hardware Design
University of Colorado System
Skills you'll gain: Cryptography, Theoretical Computer Science, BlockChain, Security Engineering

Google
Skills you'll gain: Network Security, Python Programming, Linux, Cloud Computing, Algorithms, Audit, Computer Programming, Computer Security Incident Management, Cryptography, Databases, Leadership and Management, Network Architecture, Risk Management, SQL

Google
Skills you'll gain: Computer Networking, Network Architecture, Network Model, Networking Hardware, Network Analysis, Computer Architecture, Critical Thinking, Problem Solving, Communication, Human Computer Interaction, Network Security, Linux, System Security, Cloud Computing, Computer Programming, Customer Support, Cryptography, Leadership and Management, Operating Systems

Multiple educators
Skills you'll gain: Computer Security Incident Management, Leadership and Management, Risk Management, Cloud Computing, System Security, Computer Networking, Cloud Storage, Operating Systems, Network Security, Cloud Platforms, Network Architecture, Networking Hardware, Cloud Applications, Cloud Infrastructure, Computer Programming, Cyberattacks, Databases, DevOps, Security Engineering, Cryptography, IBM Cloud, Software Engineering

Skills you'll gain: Cloud Computing, Computer Networking, Cloud Storage, Customer Success, Operating Systems, Leadership and Management, System Security, Strategy and Operations, Cloud Applications, Cloud Infrastructure, Cloud Platforms, Communication, Computer Programming, Cyberattacks, Customer Support, Databases, DevOps, Networking Hardware, Cryptography, IBM Cloud, Information Technology, Network Architecture, Network Security, Security Engineering, Software Engineering

Skills you'll gain: Cloud Computing, Computer Networking, Cloud Storage, Operating Systems, System Security, Cloud Applications, Cloud Infrastructure, Cloud Platforms, Cyberattacks, Databases, DevOps, Networking Hardware, Computer Programming, Cryptography, IBM Cloud, Network Architecture, Network Security, Security Engineering, Software Engineering

Skills you'll gain: Cryptography, Python Programming, Linux, Network Security, Security Strategy, Software Security, System Software, Computer Security Incident Management, Networking Hardware, Security Software, Cloud Computing, Cyberattacks, DevOps, Mobile Security, Computer Programming, Databases, Leadership and Management, Operating Systems, SQL, System Security

Skills you'll gain: Cryptography, Network Security, Linux, Networking Hardware, Security Software, System Software, Cloud Computing, Cyberattacks, Databases, Leadership and Management, Operating Systems, SQL, System Security

University of Pennsylvania
Skills you'll gain: FinTech, Finance, BlockChain, Innovation, Investment Management, Financial Management, Financial Analysis, Risk Management, General Statistics, Payments, Algorithms, Banking, Behavioral Economics, Entrepreneurial Finance, Market Research, Cryptography, Human Learning, Machine Learning Algorithms, Machine Learning Software, Securities Trading, Applied Machine Learning, Machine Learning, Product Strategy, Business Transformation, Systems Design

Skills you'll gain: Cryptography, Linux

Skills you'll gain: Communication, Computer Networking, Computer Architecture, Network Security, Operating Systems, Networking Hardware, Security Engineering, Network Architecture, Software Security, Human Computer Interaction, Security Software, Software-Defined Networking, System Software, Theoretical Computer Science, Cloud Computing, Data Management, Computational Logic, Network Model, Customer Support, System Security, Security Strategy, Cryptography, Problem Solving, Programming Principles, Adaptability, Linux
In summary, here are 10 of our most popular cryptographic hardware courses
- Hardware Security: University of Maryland, College Park
- Cryptographic Hash and Integrity Protection: University of Colorado System
- Google Cybersecurity: Google
- Google IT Support: Google
- IBM and ISC2 Cybersecurity Specialist: ISC2
- IBM IT Support: IBM
- Information Technology (IT) and Cloud Fundamentals: IBM
- IBM Cybersecurity Analyst: IBM
- IT Fundamentals for Cybersecurity: IBM
- Fintech: Foundations & Applications of Financial Technology: University of Pennsylvania










